Google Cloud has introduced a Cryptomining Protection Program, offering up to $1 million in coverage for unauthorized compute expenses resulting from undetected crypto mining attacks, demonstrating their commitment to enhancing security measures and mitigating the financial risks associated with such attacks.
Google Cloud, one of the leading cloud computing providers, has recently taken significant steps to bolster its security offerings by incorporating cryptomining attack prevention into its risk-management solution and Security Command Center Premium service.
This move comes in response to the rising threat of undetected cryptomining, which have proven to be a serious concern for organizations globally.
Google Cloud is offering up to $1 million in coverage for unauthorized expenses aiming to provide customers with enhanced protection and peace of mind.
Detecting and Preventing Crypto Mining Attacks
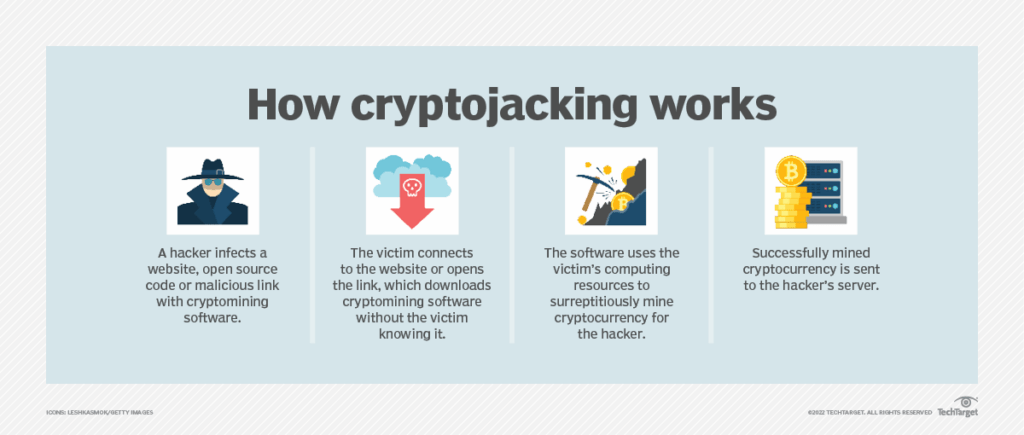
Crypto miners, unlike their more noticeable ransomware counterparts, tend to operate stealthily within victims’ computing environments. They gain unauthorized access, often through compromised credentials, and silently deploy mining malware to exploit computing resources for cryptocurrency mining.
Google Cloud’s Cryptomining Protection Program is designed to swiftly detect and halt such attacks. The program is integrated into the Security Command Center Premium, Google Cloud’s security and risk-management platform. It employs advanced techniques, including scanning virtual machine memory for mining malware, without relying on performance-degrading agents.
Financial Protection for Customers
To demonstrate their confidence in the effectiveness of their cryptomining detection capabilities, Google Cloud is offering a substantial financial safeguard. Customers subscribed to Security Command Center Premium can avail themselves of coverage up to $1 million for unauthorized compute expenses resulting from undetected cryptomining attacks.
If the premium service fails to identify and notify customers of an ongoing crypto mining attack, affected customers can request credits within 30 days to cover the unauthorized Compute Engine costs. Google Cloud works closely with customers to determine the expenses incurred, ensuring that the maximum credit limit does not exceed $1 million in any 12-month period.
The Growing Threat of Crypto Mining Attacks
Google’s own Cybersecurity Action Team revealed that 65% of compromised cloud accounts experienced cryptocurrency mining. The attackers behind these operations exploit stolen computing resources for mining popular cryptocurrencies like Monero (XMR).
The illicit nature of crypto mining, coupled with its ability to generate substantial profits, makes it an attractive avenue for cybercriminals. If left unchecked, these attacks can lead to unauthorized computing costs soaring into hundreds of thousands of dollars within a matter of days.
Responsibilities and Limitations
While Google Cloud assumes responsibility for detecting and notifying customers of these attacks, the response and remediation actions lie with the customer. This means that customers must promptly take appropriate measures to mitigate the impact of the attack and prevent further exploitation.
The Cryptomining Protection Program exclusively covers Compute Engine Virtual Machine types and supported compute environments under the Security Command Center Premium’s Virtual Machine Threat Detection. Other Google Cloud services are not included within the program’s scope.
Final Thoughts
Google Cloud’s introduction of crypto mining attack protection, backed by its Cryptomining Protection Program, showcases the company’s commitment to strengthening the security posture of its customers. The company aims to provide a robust defense mechanism and financial coverage against the potential financial and operational damages caused by these stealthy cyber threats.
As the prevalence of crypto mining attacks continues to grow, enterprises can now leverage the company’s advanced detection capabilities and substantial protection to fortify their cloud environments and safeguard their computing resources.










