Bitcoin is one of the longest-surviving cryptocurrencies and is also the King of crypto space. Since 2010, BTC has thrived despite the numerous crackdowns that have been issued on it. But do you really understand what Bitcoin is and everything about it? Some do, but many don’t. The crypto industry is the youngest in the finance and tech world.
With a total market cap of just about $1 trillion, the majority of the world has not yet been onboarded to the crypto space. If you are reading this, you probably want to understand Bitcoin deeper. Ready to become a Bitcoin wizard? Let’s dive in.
You will need a Wallet Address Before Anything
In Bitcoin, everything starts with the keys and there are three different types of keys:
- Private Key
- Public Key
- Address
Private Key
The private key is the first to be generated randomly using a mathematical process that enables different unique private keys for each generation. A 256bit 1077(abnormally large) number is introduced into the SHA256 algorithm. The result is the private key.
Generating two similar private keys is like randomly choosing two people among all human beings who exist and these two people happen to have exactly the same genome. It’s IMPOSSIBLE!
The private key is picked randomly among an infinitely large set in order to avoid generating the same one twice. Therefore, a large source of entropy is needed, and hence why environmentalists dislike BTC.
For the paranoid, here is a simple Python script to generate your own private key, public key, and public address.
| from bitcoin import *private_key = random_key() private_key_hex = decode_privkey(private_key, ‘hex’) #private key hex format private_key_wif = encode_privkey(decoded_priv_key, ‘wif’) #private key wif format public_key = fast_multiply(G, private_key_hex) #elliptic curve multiplication public_key_hex = encode_pubkey(public_key, ‘hex’) #public key hex format address = pubkey_to_address(public_key_hex) |
Public Key
The public key is generated from the private key with elliptic curve cryptography (ECC). This function has only one direction that enables you to calculate f(x) according to x (where x is the private key), but makes it impossible to pass from f(x) to x. Does your head hurt? Here, let me try to simplify it for you.
Imagine you have two friends, Alice and Bob, who want to send secret messages to each other. But they don’t want anyone else to be able to read those messages. So they need a special way to protect their messages. Elliptic curve cryptography is like having a magic lock and key that only Alice and Bob can use. The magic lock is a special curve.
Alice and Bob each have their own special secret numbers that act like their own special keys. When Alice sends a secret message to Bob, she uses her secret number with the ECC curve. When Bob receives the message, he uses his secret number with the ECC to unlock and read the secret message.
So with elliptic curve cryptography, Alice and Bob can send secret messages to each other using their special secret numbers and the magic lock. No one else can understand their messages because they don’t have the right keys. It’s like having a secret language that only they can understand.”
Public Address
The public address is generated from the public key using a hash function which is also one-way. The public address is the information given to receive BTC while the private key is what unlocks the BTC present in the corresponding public address.
The first Bitcoin wallets were physical cards with a private key (to spend) on one side and the address (to receive) on the other side, very simple. However, these were not secure.
You Can’t Have a wallet Address without a Wallet
A wallet is simply an application that enables you to manage keys and addresses, track balances, create transactions, and sign transactions. It does not contain BTC, only the private keys that enable signing transactions that unlock BTC from the blockchain. There are two types of wallets:
- Nondeterministic Wallets
- Deterministic Wallets
Nondeterministic Wallets
These types of wallets generate a set of random private keys that have no relation to each other. since the private keys have no relationship to each other, an efficient backup system is necessary. It makes the wallets hard to use and therefore not widely used. Not much to be discussed here.
Deterministic Wallets
These types of wallets generate private keys from the seed, so all private keys are linked and can be regenerated from the seed. Also called Heuristic Deterministic (HD) wallets, deterministic wallets facilitate use and backup and hence they are the most popular and widely used wallets.
The seed is often transformed into Mnemonic Codes (12/24 words) using the BIP-39 standard. These are easier to transcribe, record on paper, and read without errors.
SafePal is a great example of an HD wallet because, upon first use, you must record the Mnemonic phrase to restore all private keys if necessary. SafePal has both cold and hot wallet options, but both are heuristic deterministic wallets
Cold Wallets
A cold wallet stores private keys offline, away from any internet connection. Therefore, even if a hacker gains access to your computer or smartphone, they cannot access your cold wallet and steal your private keys.
Hot Wallet
A hot wallet uses a storage method connected to the internet to store private keys. They are often used for regular transactions as they are easily accessible and can be used to send or receive BTC quickly. Hence they are more practical but less secure.
Are You Ready to Send Your First Bitcoin?
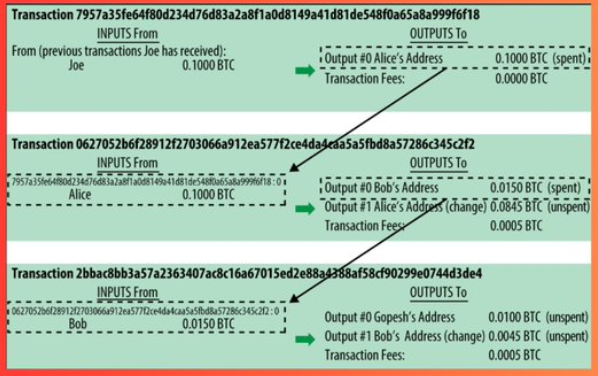
Transactions are the most important parts to understand since each transaction creates unspent transaction outputs (UTXO) that can be used as inputs for future transactions. Therefore, on Bitcoin, you do not actually spend BTC. Instead, you spend unspent transactions (UTXO).
Transactions in the Bitcoin network do not look like those of other blockchains. For example:
Suppose Alice sends 0.015 BTC to Bob and pays 0.0005 BTC in gas fees. Since on Bitcoin we spend UTXOs, Alice spent her “vin” UTXO to create two more UTXOs in “vout”. Alice has a UTXO worth 0.1 BTC, so in order to pay Bob she must create two UTXOs, one for Bob (0.015 BTC) and one for her (her balance).

- vin: the UTXO that Alice received from a previous transaction and has just spent.
- Txid: A transaction ID, referencing the transaction that contains the UTXO being spent
- vout: An index identifying which UTXO from that transaction is referenced (the first one is zero)
- scriptSig: which satisfies the conditions placed on the UTXO, unlocking it for spending
- sequence: used for lock time
Transaction fees are not explicitly defined in the transaction. They are determined by differentiating between the sum of inputs and the sum of outputs. If Alice had not included an output back to herself (for her balance), she would have paid 0.085 BTC in transaction fees.
Note: One UTXO is divided into two or more UTXOs during each transaction.
Conclusion
Bitcoin is a complex network and this is just the gist. There are a lot of people who are in the cryptocurrency ecosystem but don’t understand how Bitcoin works, it’s unfortunate, Bitcoin is at the center of this ecosystem. By understanding how Bitcoin works, you will understand more easily everything that is developed in DeFi, including BRC20, STAMPS, SRC20, and Ordinals – it will make everything that follows easier for you.










